Complete Cyber Forensics Notes for B.Tech CSE students covering Unit 1 to Unit 6. Learn cybercrime, digital forensics, incident response, forensic duplication, network forensics, forensic tools, email investigation, mobile device forensics, Windows systems, NTFS file systems, encryption, registry analysis and cyber laws including IPC, CrPC and Indian Evidence Act.
Unit 1 – Introduction to Cybercrime and Digital Forensics
Cybercrime refers to criminal activities carried out using computers, networks or the internet. Examples include hacking, identity theft, phishing, cyber stalking and malware attacks.
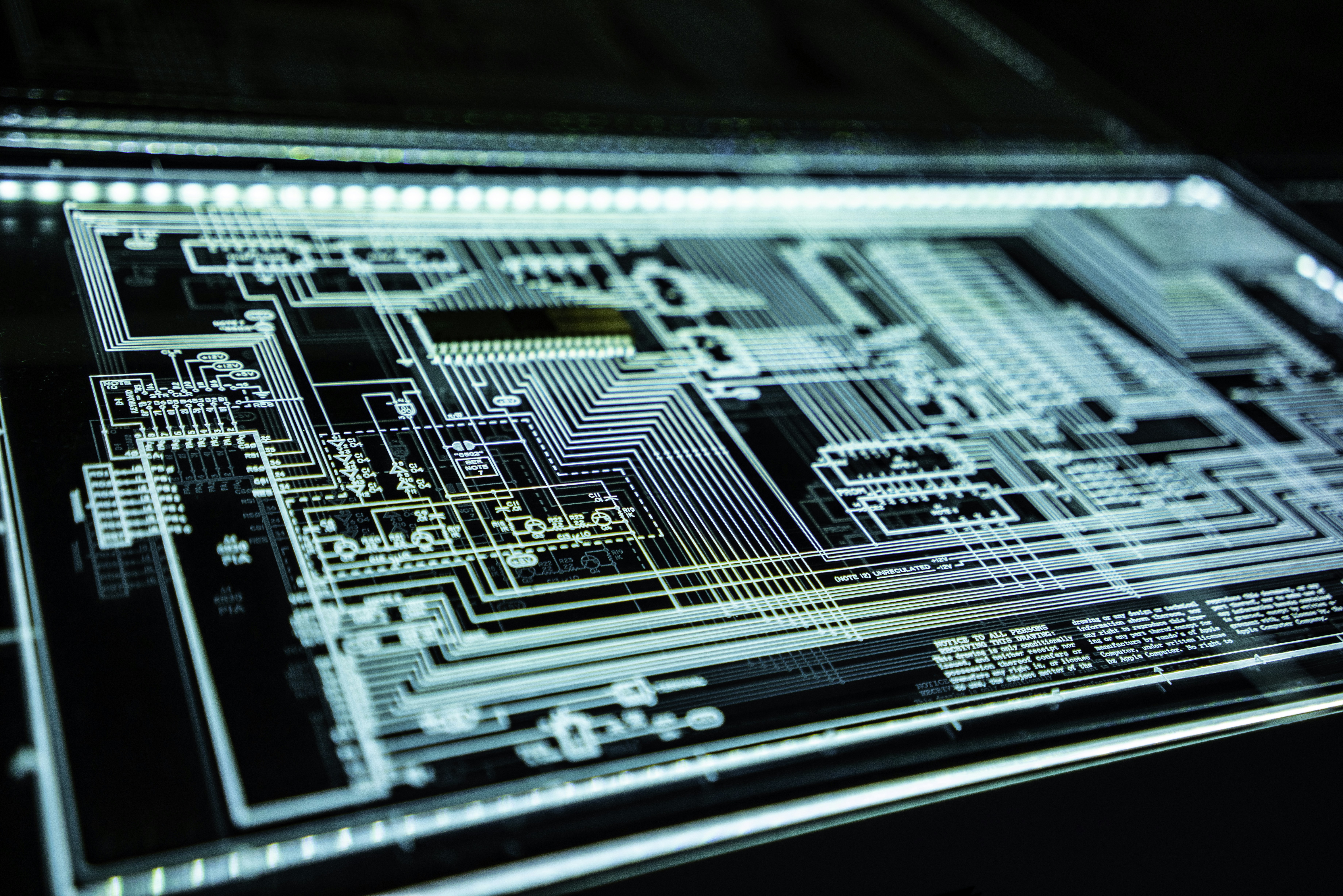
Digital forensics is the process of identifying, collecting and analyzing digital evidence from devices like computers, mobile phones and servers.
Unit 2 – Initial Response and Forensic Duplication
The initial response is the first action taken when a cyber incident occurs. Investigators must secure the system, collect volatile data and prevent evidence destruction.
Forensic duplication involves creating an exact copy of a hard disk without altering the original evidence.
Unit 3 – Forensic Analysis and Network Forensics
Forensic analysis focuses on examining digital evidence to identify cyber attacks, malware and unauthorized access.
Network forensics investigates network traffic, logs and communication patterns to detect cybercrime.
Unit 4 – Current Forensic Tools and Email Investigation
Various forensic tools help investigators analyze digital evidence including disk images, emails and system logs.
Email investigation involves analyzing sender information, email headers and server logs to trace cyber criminals.
Unit 5 – Working with Windows and File Systems
This unit focuses on understanding Windows operating systems, file systems such as NTFS, disk encryption, Windows registry and startup processes.
Investigators analyze these components to detect hidden files, malware activity and system modifications.
Unit 6 – Cyber Laws and Legal Aspects
Cybercrime investigations must follow legal procedures to ensure digital evidence is admissible in court.
Important laws include:
- Indian Evidence Act
- Indian Penal Code (IPC)
- Criminal Procedure Code (CrPC)
- Electronic Communication Privacy Act
These laws define how digital evidence should be collected, preserved and presented during legal proceedings.
Why Cyber Forensics is Important
- Helps investigate cybercrime
- Protects digital information
- Supports legal investigations
- Improves cybersecurity defense
Conclusion
Cyber Forensics plays a critical role in modern cybersecurity investigations. By understanding cybercrime, digital evidence handling, forensic tools and cyber laws, students and professionals can effectively analyze cyber incidents and contribute to a safer digital environment.